DailyPost 1943
LEAKED SITES – A NEW FACET OF RANSOMWARE
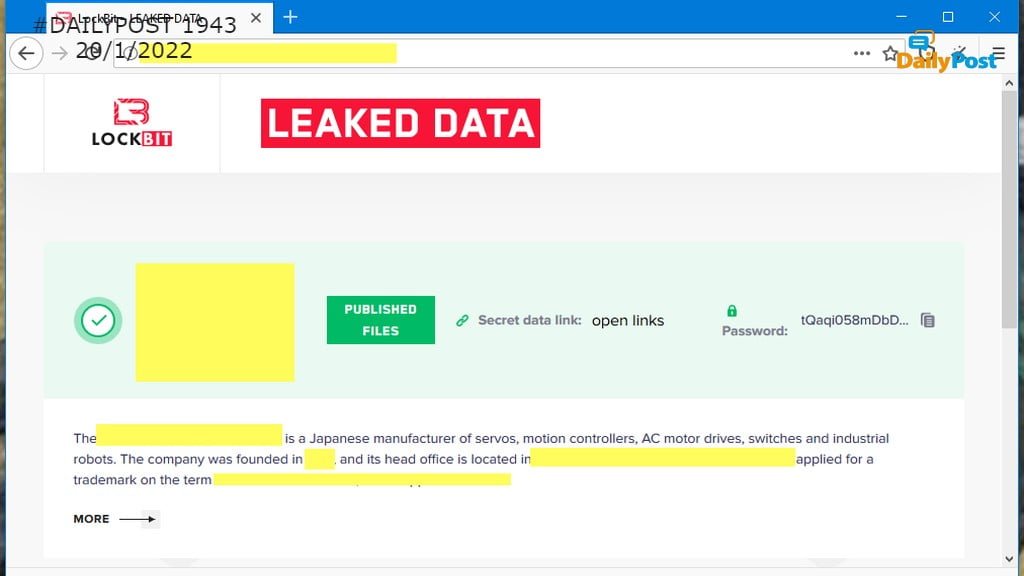
Restricting ransomware to ransom has already become something of the past, as ransomware rages the world as another pandemic, ripping apart businesses, utilities and critical infrastructure. The faith in our capability to run our own digital systems is today at its lowest ebb. Cyber criminals are lurking from every nook and corner and ransomware attackers rule the roost. The ransom runs into millions of dollars but that is the only method to generate money out of a ransomware attack. Now ransomware operators are not happy only with encrypting files on site and discretely charge their victims money for a decryption key. Leaking the data is now an additional threat. This is what is now termed as the Double Extortion, it is also known as Cyber Extortion or Cy-X.
Taken from a criminal perspective is it a unique form of crime, where extortion is orchestrated through what is called a Leaked Site and more often than not it is on the DarkNet. You may call it a Dark Site as well. Some of the criminal action is conducted by the process termed as ’victim shaming.’ An analysis of these leaked sites since Jan 2020 by identifying them and record and document the victims who feature in them throws up some interesting facts. By this analysis and by enriching data scraped from various Cy-X sites, one is able to reach direct insights into the victimology from this limited perspective. Undoubtedly, the listing of a compromised organization on a Cy-X leak site is a ”leak threat.”
Appearing on Onion sites, they have been tracked for the last two years, in this research. ”the number of unique leaks serves as a reliable proxy for the scale of this crime, and its general trends over time.” This analysis has observed that there has been almost a six fold increase from the first quarter of 2020 to the third quarter of 2021. How does it correspond with us getting into the pandemic age and getting fully immersed in digital technology for our very survival. The research shows that the top victim countries have remained constant across the dataset. There is correlation with the GDP of the country. Bigger the economy, more victims come from it and 8 out of the top victim countries are among the top ten economies in the world.
Size of businesses or the open threat surfaces provide the bigger opportunities for ransomware, needs further research. It also necessitates a study to find out the correlation between cyber security measures and landing into the dual situation of outright ransomware and getting into the plight of Double Extortion. Any action on these sites still remains in the territory of the unknown. Are the LEAs in possession of handling this nature of crime. India, China, Japan and Russia are counterexamples to the Big Economy and the Leaked Sites connection. In India it can be because of lower per capita GDP and the economy being less digital. The criminals feel that dollar-based ransoms would not be forthcoming. Besides, the language may be a barrier as in the case of China and Japan. The final thought is that victims are found in every country, and ”countries who have hitherto appeared unaffected cannot hope that this will remain the case.”
LEAKED SITES TURN OUT TO BE A SERIOUS ONSLAUGHT ON THE BUSINESS ENTERPRISE.
Sanjay Sahay