DailyPost 655
EVERYDAY DEVICES CONUNDRUM
While we hear of big hacks and breaches on a regular basis but the threat on a general basis is more from the everyday devices we use. Actually, in the overall security stance, deliberate practice and thoughtful approaches to security increases the protection of your business & workplace. Your investment in antivirus, firewalls & regular security updates is not enough.
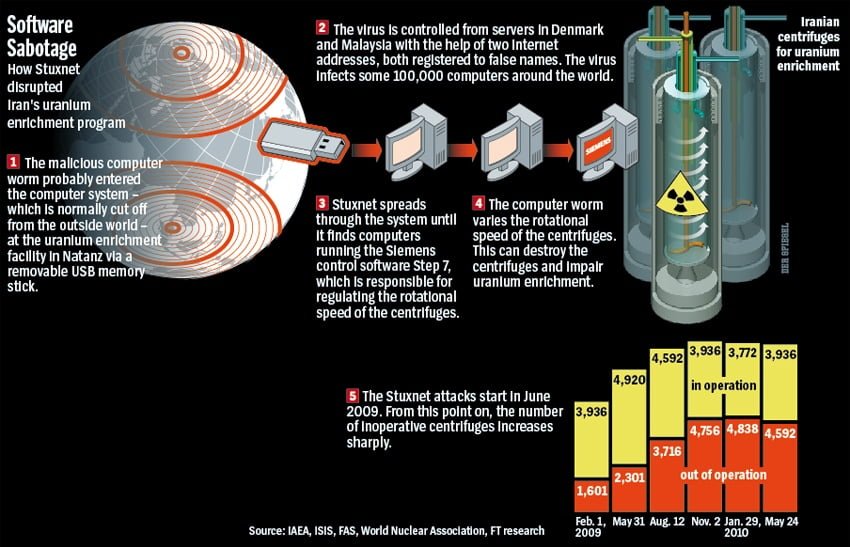
USB supply chain attacks is a important threat vector. An attack on the classified military system is unexpected as it is not connected to outside networks. But the attack has happened. In one of the instances the source was isolated to worm loaded onto a USB key that had been carefully set up. It was left in large numbers to be purchased from a local internet kiosk. This is one example of the supply chain attack. It focuses on the least secure element of the supply chain.
In an understandable reaction the US military moved to ban the USB drives in the field. What they learned form this experience came to their rescue a few years later. US used the same tactic to breach and disrupt Iran’s nuclear weapons program in an attack, that has now been dubbed as Stuxnet. It’s the 9/11 of Cyber Security. Lesson is for USB one should be sure where it comes from and whats on it. You can currently buy a USB stick that is secretly a small computer. On insertion it will open up a window on your machine and play the Death Star march.
In the network environment of today, information assets are concentrated, one computer compromised is enough. In 2012, 16 versions of Cisco popular IP phone was transformed into a listening device. In 2017, a similar issue arose when a brand of hospital grade dishwasher was affected by a built-in insecure web server. Experts attribute supply chain attacks in the disastrous failure rate of the North Korean missile program.
WITH THE CURRENT RATE OF EVERYDAY DEVICES, THE VULNERABILITY INCREASES DISPROPORTIONATELY.
Sanjay Sahay