DailyPost 379
WHITE HATS
Even to the ignorant & the uninitiated WannaCry & Petya global level hacking epidemic, made them aware of the immense damages the hackers can do. There is a general perception that hackers can breach systems at will and the gap between their expertise, focus, effort & precision and of the enterprises mandated to safeguard is wide. Not only that, it is increasing with every passing day. The cyber security researchers have been of use at the time of WannaCry attack but can that be pushed through as the only & as a comprehensive solution. The answer is NO in bold.
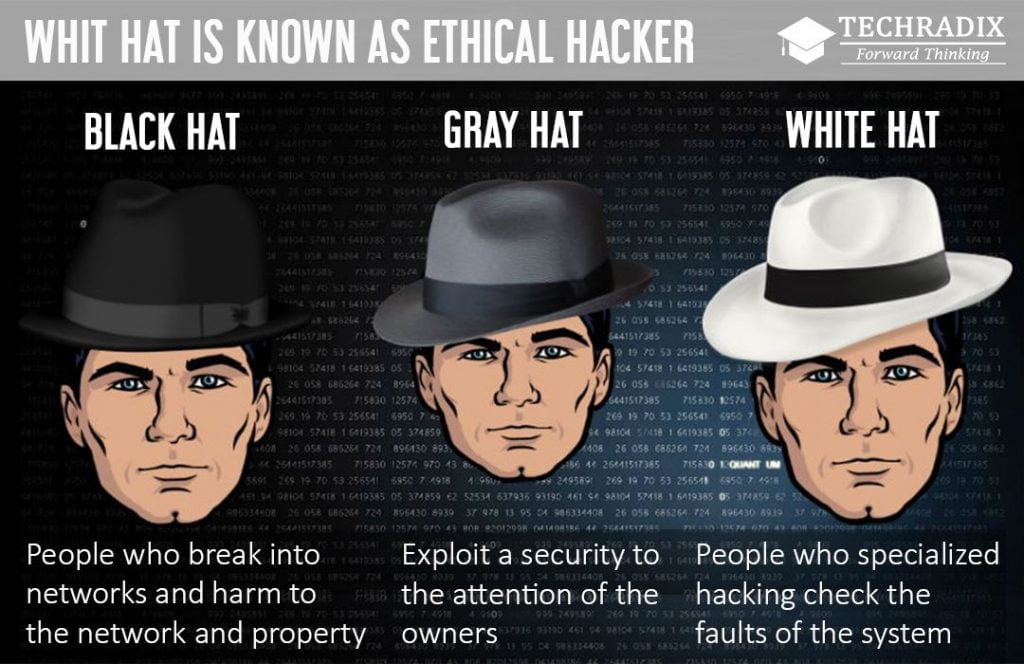
The hackers in different colours of Hats, as per the Internet slang. A black hat hacker is a hacker who ”violates computer security for reason beyond maliciousness or for personal gain.” The grey hat hacker sometimes violates laws or typical ethical standards but does share the motives of a Black Hat hacker. The White Hat Hacker, is an ethical computer hacker, to ensure security of an organisations computer systems. Ethical hacking term was coined by IBM. The White Hat Hackers are variously termed as sneakers, red teams & tiger teams . Black Hats are most known of the lots and conduct one of its conferences, which the whole of the computer world watches. Hacktivists are another category, Julian Assange / Edward Snowden et al, can be hugely damaging.
As per New York Times White Hat activities as one of “ mischievous but perversely positive ‘hacker’ tradition.
One of TED Talks calls hackers as the bulwark of the Internet’s Immune System. White Hat Hackers have proved their worth over & over again in individual cases but are not a force to reckoned with as the Black Hat counterparts. Given the nature of all pervasive breach issues we face, they can be the only saviours . They have to become a part of our structured existence. We have to keep them inspired.
If the bad guys can do it, why can’t the good guys. This change has to happen now.
WHITE HAT HACKERS CAN POSITIVELY IMPACT THE CYBER SECURITY SCENARIO.
Sanjay Sahay